Blog
Top 10 Overlooked User Experience Best Practices in Design
User experience (UX) design is an important aspect of creating successful digital products. However, despite its importance, some crucial UX best practices are often overlooked in the design process. In this blog post, we will discuss ten often-overlooked UX best...
Why OTPs shouldn’t be part of a passwordless strategy
One-time passwords (OTPs) are a common way to add an extra layer of security to an authentication process, but they can still be vulnerable to attacks and are not recommended as a sole means of authentication in a passwordless strategy. OTPs rely on the assumption...
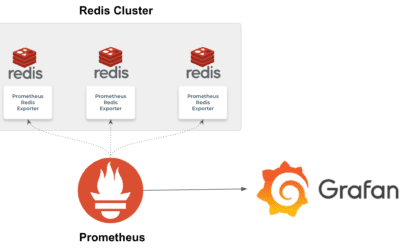
Monitoring REDIS using Prometheus and Grafana
Redis is a popular open-source in-memory database which can also be used as a message broker. It can be scaled (lineraly) to handle large volumes and throughputs of an order of 50 million ops per second. Redis can be considered as a key-value store, but the uniqueness...
Understanding Consumer Groups and Partitions in Kafka
In a typical modern enterprise, there would be multiple systems producing data in different formats and multiple systems which has to consume these data. Integrating these systems using a full mesh topology will be complicated owing to the myraid of protocols...